MacOS-apparaten onboarden naar Microsoft Purview met behulp van Microsoft Intune
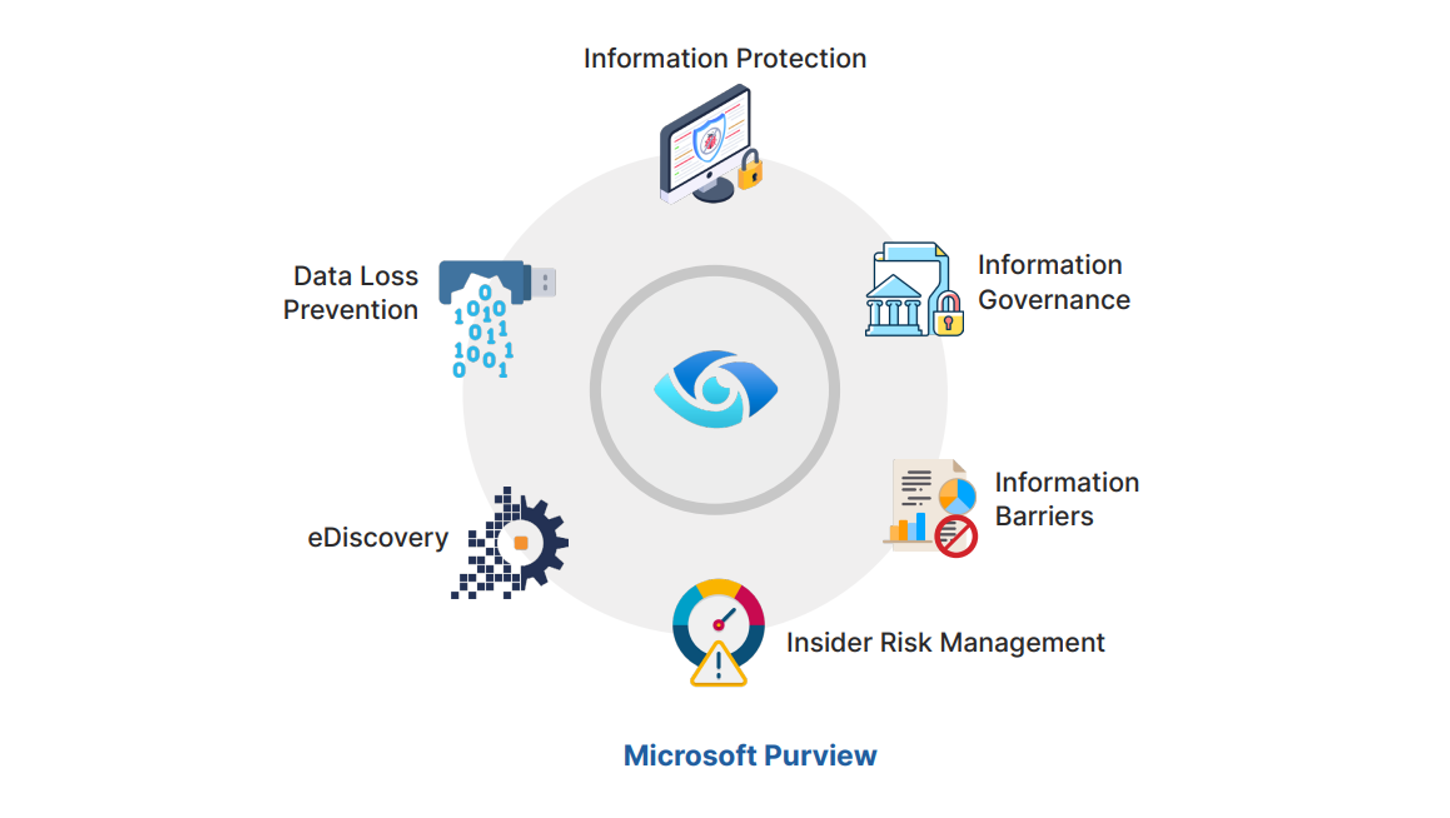
Zoals eerder vermeld, moet een succesvolle DLP-implementatie alle 3 de belangrijkste gegevensexfiltratiekanalen omvatten, namelijk Web, Samenwerking applicaties (Teams, Sharepoint. OneDrive)…
Bescherm Uw E-mails Met Antispam, Anti-phishing, SPF, DKIM en DMARC
In het huidige digitale landschap blijft e-mail een cruciaal communicatiemiddel voor organisaties. Het is echter ook een primair doelwit voor…
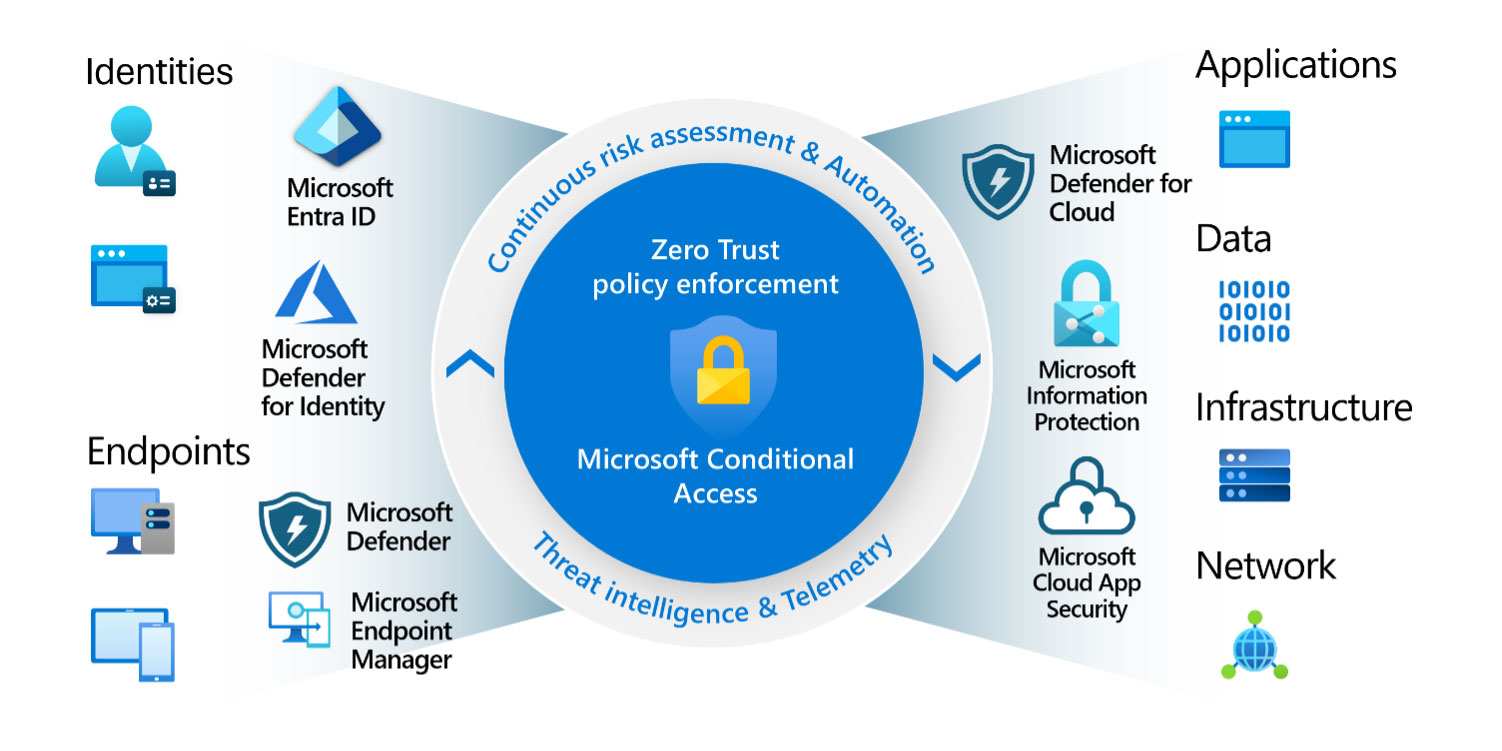
Deployment of 10 Essential Conditional Access Policies
Deploying Conditional Access in your organization can be (and should be) a rather long task. This is because rushing into…
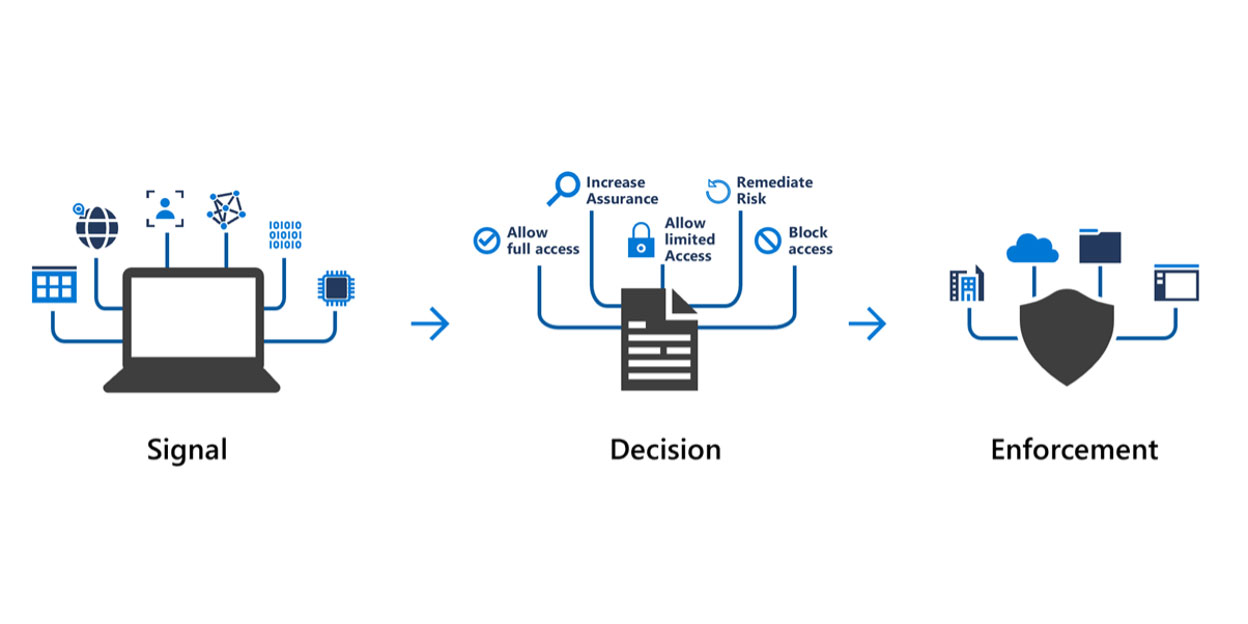
Introduction to Conditional Access
Introduction to Conditional Access More and more applications are made available to the users on public internet with organizations embracing…
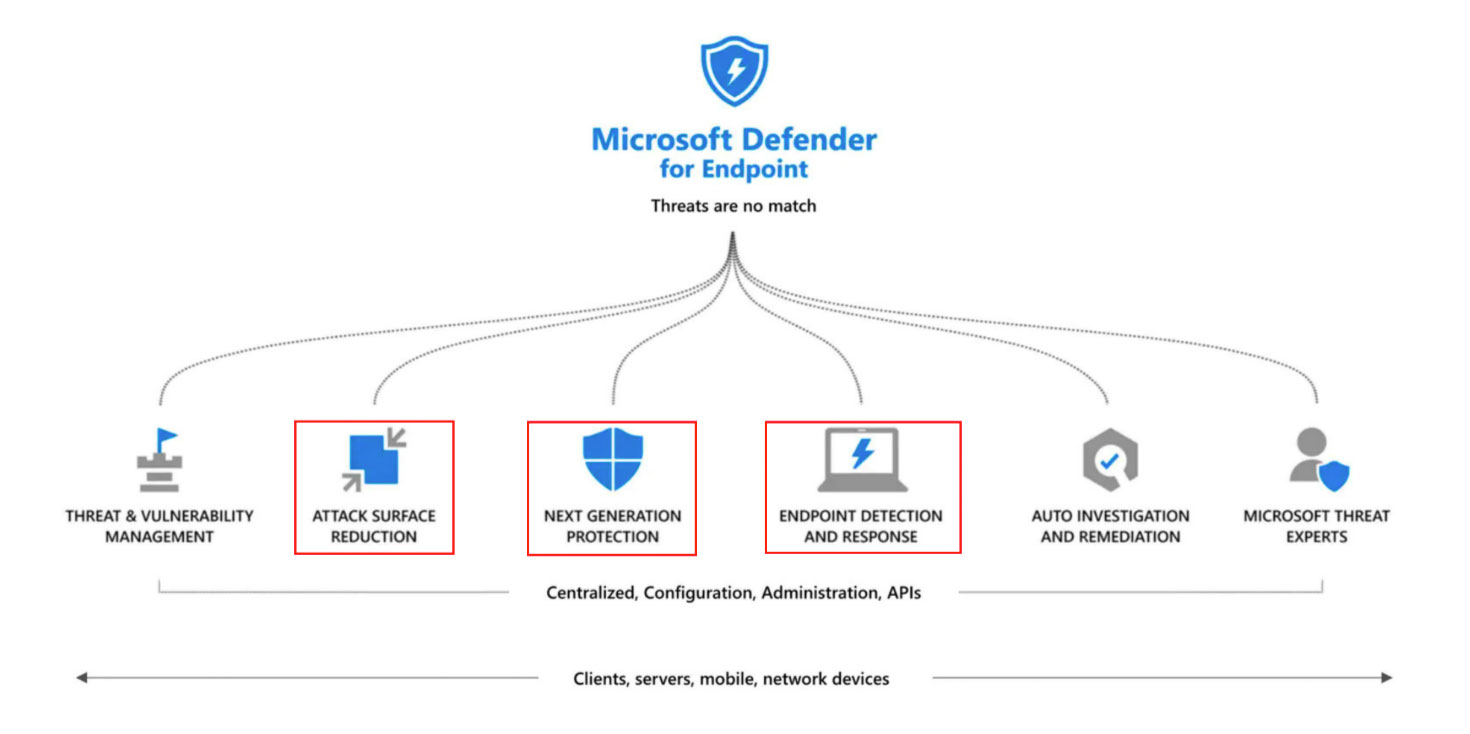
Microsoft Defender for Endpoint Attack Surface Reduction
What is ASR? One of the capabilities of Microsoft Defender for Endpoint that is often overlooked because of its fancy…